NetOris Version 3 - The Network Controller
NetOris can be used to control any windows system.
Usage :
- There are two pieces of Software NetOris Client and NetOris Server.
- NetOris Client is the backdoor which you should give to the victim.
- Once the Victim opens the Client it automatically installs and Starts running.
- Now trace the IP address of the Victim. (U can trace the IP if your a hacker or just google).
- Fire the NetOris Server and put Victim's IP address in IP Address box and Click Connect.
- Then You'll be connected to the Client.
- Now start using their computer as its yours.
New Features :
- Added GUI replacing the old CLI.
- File Manage (Send and Receive files).
- Send different types of messages.
- Block mouse instead of hide mouse.
- Power Sucking which executes until you stop (Power sucking switches off the monitor forever).
- Capture the screen of the Victim.
- Remote Shell with copying enabled (CTRL + C).
- Update Notifier.
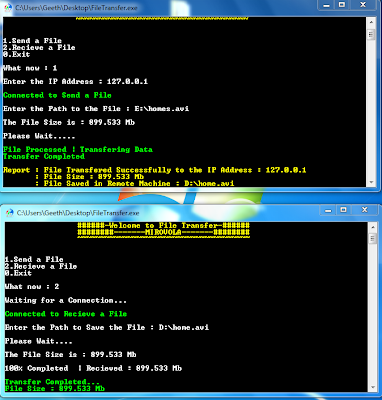
Send Files to Computers Directly
You Have a File to Send your friend ? Don't know how to send Directly ?
Download this Simple Program and It will do it for you!!!
- To Send the file Open the File Transfer Program and Select Send a File.
- Enter the IP Address.
- Ask Receiver to Select Receive in the Program.
- Once Connected You can send the File.
List Running Tasks and Kill them with CMD
- Open the CMD (Command Prompt) and Type in "tasklist" without quotes and hit enter.
- All the running Processes will be displayed here.
- To kill a Process you can use "taskkill" command without quotes.
- Type tasklist /F /PID <PID of Application to kill>
- For Example : If I want to kill DTLite.exe in the below image then Type
tasklist /F /PID 2136
- You can see that the DTLite no more exists in the Running Tasks.
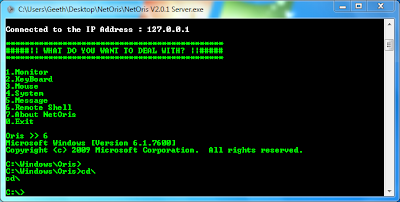
NetOris Version 2.0
The Network Controller
Control Your Friend's Computer as its Yours.
Features :
1.Monitor
- Switch Off the Monitor
- Power Sucking (Switches off the Monitor Continuosly for 9 Times)
2.KeyBoard
- Perform Alt+F4 Key Press
- Record Key Strokes
3.Mouse
- Randomize the Mouse
- Hide the Mouse
4.System
- Open/Close CD ROM
- Shutdown the Computer
- Restart the Computer
- Log Off the Computer
- Add User
- Remove User
- Disable Firewall
- Execute a File
5.Messages
- Information Messages
- Warning Messages
- Exclamation Messages
6.Remote Shell
Get a Shell to the Remote System. That's all Every Hacker needs ?
How to Use
There are two pieces of Software Client and Server
- First Upload the Client to a Free Hosting Service but Remember to Rename it to a cool name before upload so the Victim Should Believe.
- Ask him to Download and open the Client. Once he Open it the software will get installed Automatically. And works in the Background.
- Next Step is to Find his IP address. There are so many ways to find IP address. You can use www.whatstheirip.com to send the victim's ip to your Mail.
- Now Open the NetOris Server and input the IP address of the Victim and your Connected.
You Can Upload files to www.datafilehost.com I feel it easy.
Please Note : You Can Also Test it in your system by Opening Client file and then Open Server and input the local IP (127.0.0.1).